Enterprise-grade protection. Trusted legal AI.
Plexus protects your legal and business data with ISO 27001-certified infrastructure, advanced encryption, and secure AI built for privacy, not publicity.
/Colour/Woolies.png?width=225&height=70&name=Woolies.png)
/Colour/Cocacola.png?width=225&height=70&name=Cocacola.png)
/Colour/General%20Mills.png?width=225&height=70&name=General%20Mills.png)
/Colour/ACC.png?width=225&height=70&name=ACC.png)
Built for speed. Backed by trust.
Plexus empowers business and legal teams with advanced AI and enterprise-grade security - keeping your data private, encrypted, and always in your control.



Proactive protection for modern legal teams
Trusted by legal teams at Fortune 500 companies
Achieving the global ISO 27001:2022 benchmark for information security management systems.
In transit (TLS) and at rest (AES-256) with strict access controls and regular audits.
Safeguarding personal data with transparency and strict privacy controls.
AWS-backed infrastructure with firewalls, monitoring, and intrusion detection.
Unique user accounts, brute-force protection, and breach detection.
AI governance principles
Plexus AI enhances legal workflows while maintaining the highest standards of privacy and security:
Secure AI integration
We use OpenAI’s enterprise-grade GPT models. Your data is never used to train public AI models.
Tenant-Isolated Storage
Conversations and document context are stored in isolated databases and vector stores — ensuring zero data crossover between tenants.
Strict Data Controls
Customer data stays within your secure environment to support your use case only — never shared or repurposed.
Encryption & Access Controls
All AI operations meet AES-256 and TLS 1.2+ standards with full audit logging.
Training Protocols
Plexus AI learns only from your uploaded legal playbooks and policies, not public internet data.
Auditable AI
Every AI action is tracked and reviewable for complete accountability.
All your legal work. Secured in one platform.
Plexus is the end-to-end legal OS that unites contracts, matters, and compliance, powered by trusted AI and protected by enterprise-grade security.
Promotion Compliance
Generate compliant T&Cs and permits for every campaign in 24 hours, guaranteed.
Contract Management
Generate, negotiate and e-sign contracts with policy controls built in.
Promotion Compliance
Generate compliant T&Cs and permits for every campaign in 24 hours, guaranteed.
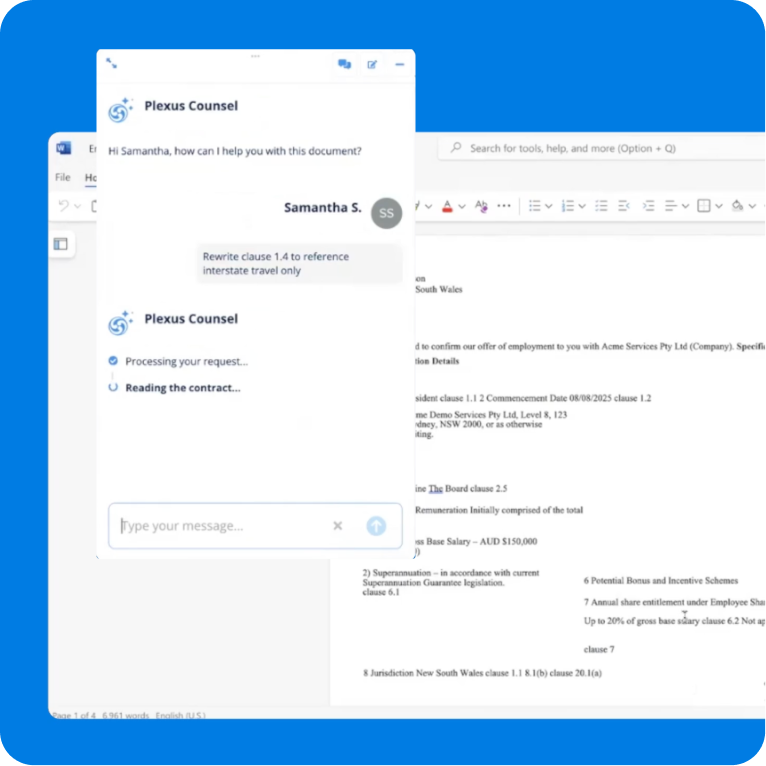
Plexus AI
Your digital lawyer that knows your business like your best lawyer, available 24/7.
Not sure where to start with AI governance?
We're here to help. Our team can show you how leading GCs use Plexus to automate oversight, simplify compliance, and build trust in every workflow.


Request security portal access
We're happy to provide access to our security documentation for customers and prospects. Complete this form and we'll send you login credentials.
Plexus AI enhances legal workflows while maintaining the highest standards of privacy and security.

CTO - Plexus